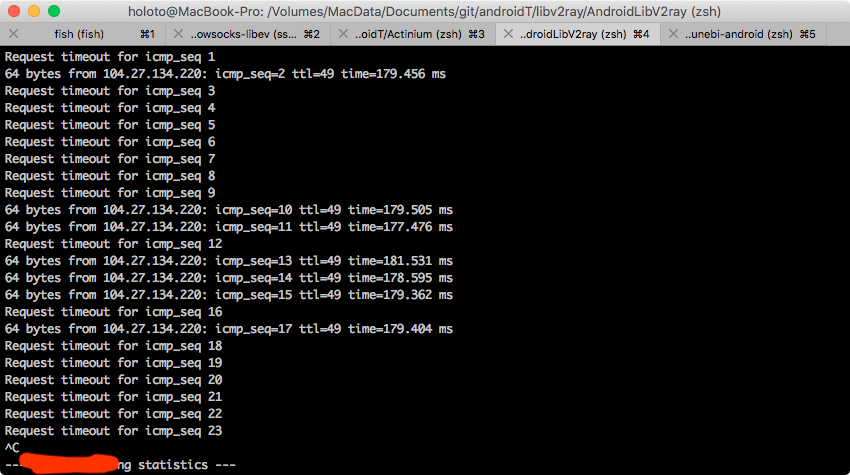
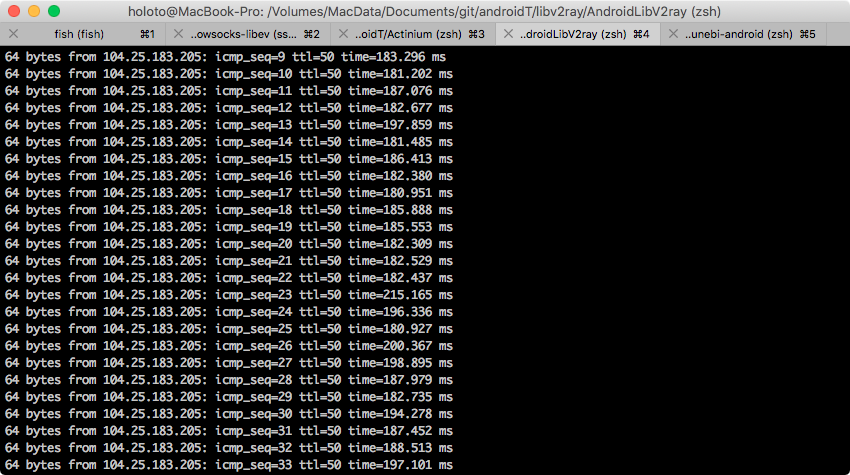
使用cloudflare 可能遇到cf分配的IP 很慢 甚者丢包
cloudflare官方IP介绍
https://www.cloudflare.com/ips/
ipv4 https://www.cloudflare.com/ips-v4
173.245.48.0/20
103.21.244.0/22
103.22.200.0/22
103.31.4.0/22
141.101.64.0/18
108.162.192.0/18
190.93.240.0/20
188.114.96.0/20
197.234.240.0/22
198.41.128.0/17
162.158.0.0/15
104.16.0.0/12
172.64.0.0/13
131.0.72.0/22ipv6 https://www.cloudflare.com/ips-v6
2400:cb00::/32
2606:4700::/32
2803:f800::/32
2405:b500::/32
2405:8100::/32
2a06:98c0::/29
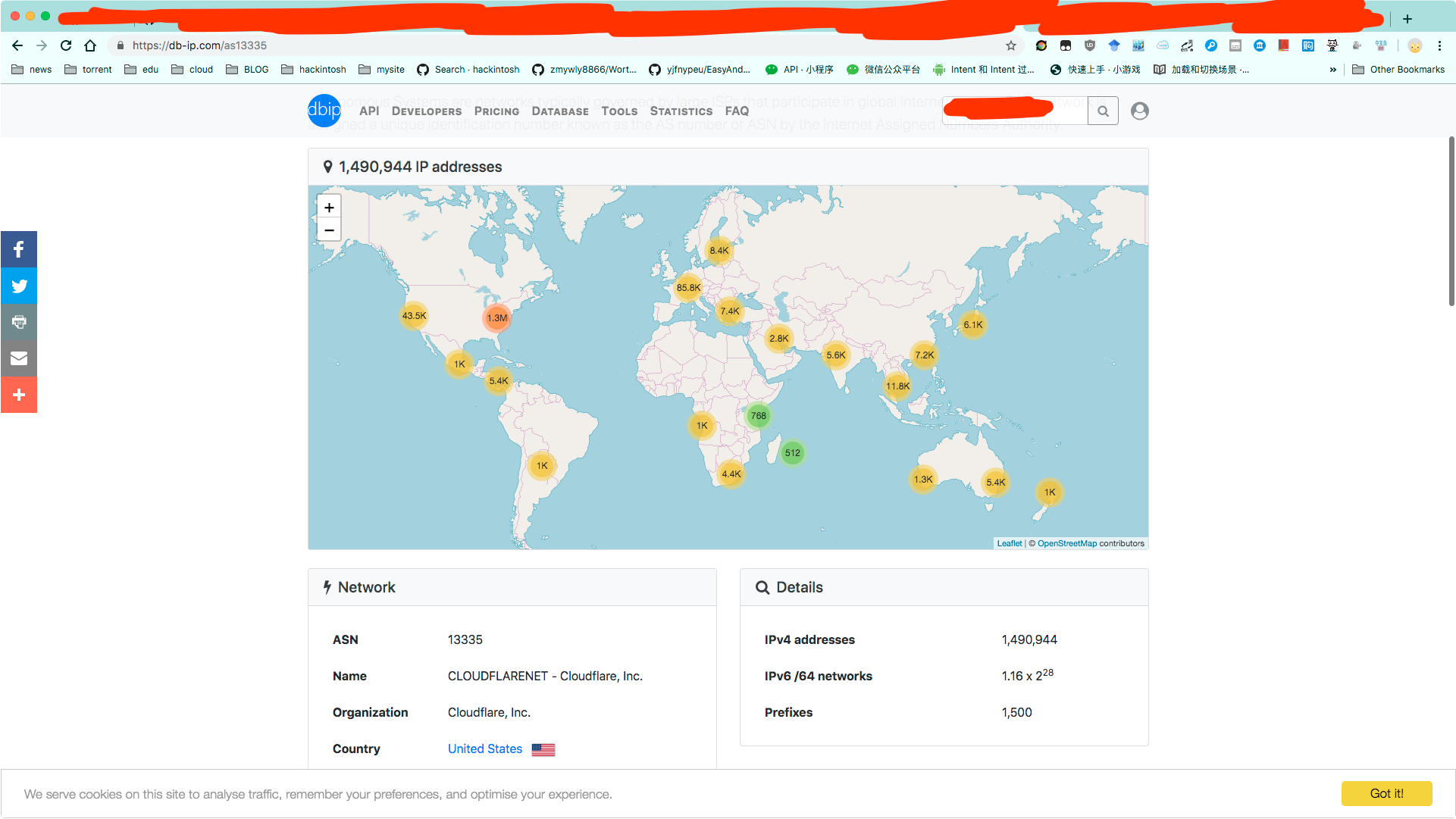
2c0f:f248::/32cloudlare ip 分布区域图
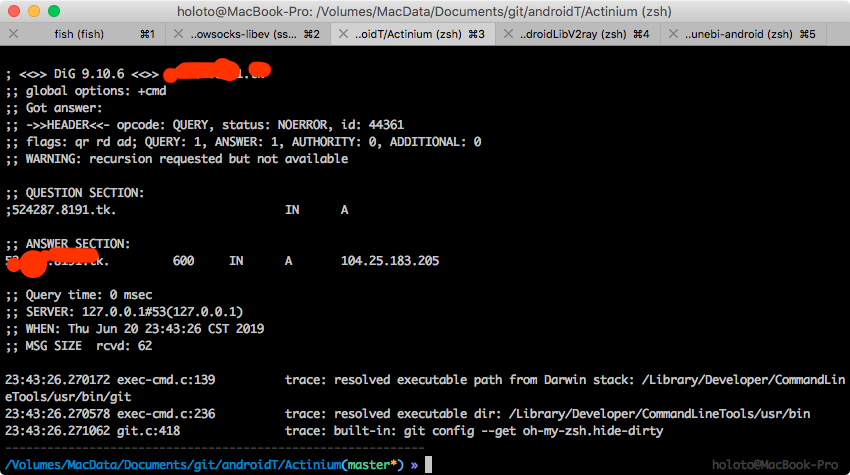
去这网站https://db-ip.com/as13335 找ip自己测试延迟把
强制解析使用cloudflare IP 解决这个问题 很好的IP网上有人分享自己搜索测试吧
这里使用dnscrypt-proxy host也可以
##############################################
# #
# dnscrypt-proxy configuration #
# #
##############################################
## This is an example configuration file.
## You should adjust it to your needs, and save it as "dnscrypt-proxy.toml"
##
## Online documentation is available here: https://dnscrypt.info/doc
##################################
# Global settings #
##################################
## List of servers to use
##
## Servers from the "public-resolvers" source (see down below) can
## be viewed here: https://dnscrypt.info/public-servers
##
## If this line is commented, all registered servers matching the require_* filters
## will be used.
##
## The proxy will automatically pick the fastest, working servers from the list.
## Remove the leading # first to enable this; lines starting with # are ignored.
# server_names = [ 'google', 'cloudflare','cisco']
# server_names = [ 'cloudflare']
# server_names = [ 'google']
## List of local addresses and ports to listen to. Can be IPv4 and/or IPv6.
## Note: When using systemd socket activation, choose an empty set (i.e. [] ).
# listen_addresses = ['127.0.0.1:53', '[::1]:53']
listen_addresses = ['127.0.0.1:53']
# listen_addresses = ['0.0.0.0:53', '[::]:53']
# listen_addresses = ['0.0.0.0:53']
## Maximum number of simultaneous client connections to accept
max_clients = 250
## Switch to a different system user after listening sockets have been created.
## Note (1): this feature is currently unsupported on Windows.
## Note (2): this feature is not compatible with systemd socket activation.
## Note (3): when using -pidfile, the PID file directory must be writable by the new user
# user_name = 'nobody'
## Require servers (from static + remote sources) to satisfy specific properties
# Use servers reachable over IPv4
ipv4_servers = true
# Use servers reachable over IPv6 -- Do not enable if you don't have IPv6 connectivity
ipv6_servers = false
# Use servers implementing the DNSCrypt protocol
dnscrypt_servers = true
# Use servers implementing the DNS-over-HTTPS protocol
doh_servers = true
## Require servers defined by remote sources to satisfy specific properties
# Server must support DNS security extensions (DNSSEC)
require_dnssec = true
# Server must not log user queries (declarative)
require_nolog = true
# Server must not enforce its own blacklist (for parental control, ads blocking...)
require_nofilter = true
# Server names to avoid even if they match all criteria
# disabled_server_names = []
## Always use TCP to connect to upstream servers.
## This can be useful if you need to route everything through Tor.
## Otherwise, leave this to `false`, as it doesn't improve security
## (dnscrypt-proxy will always encrypt everything even using UDP), and can
## only increase latency.
force_tcp = true
## SOCKS proxy
## Uncomment the following line to route all TCP connections to a local Tor node
## Tor doesn't support UDP, so set `force_tcp` to `true` as well.
# proxy = "socks5://0.0.0.0:9050"
## HTTP/HTTPS proxy
## Only for DoH servers
# http_proxy = "http://0.0.0.0:1083"
## How long a DNS query will wait for a response, in milliseconds
timeout = 2500
## Keepalive for HTTP (HTTPS, HTTP/2) queries, in seconds
keepalive = 15
## Use the REFUSED return code for blocked responses
## Setting this to `false` means that some responses will be lies.
## Unfortunately, `false` appears to be required for Android 8+
refused_code_in_responses = false
## Load-balancing strategy: 'p2' (default), 'ph', 'fastest' or 'random'
lb_strategy = 'p2'
## Log level (0-6, default: 2 - 0 is very verbose, 6 only contains fatal errors)
log_level = 6
## log file for the application
# log_file = 'dnscrypt-proxy.log'
## Use the system logger (syslog on Unix, Event Log on Windows)
use_syslog = false
## Delay, in minutes, after which certificates are reloaded
cert_refresh_delay = 240
## DNSCrypt: Create a new, unique key for every single DNS query
## This may improve privacy but can also have a significant impact on CPU usage
## Only enable if you don't have a lot of network load
dnscrypt_ephemeral_keys = false
## DoH: Disable TLS session tickets - increases privacy but also latency
tls_disable_session_tickets = false
## DoH: Use a specific cipher suite instead of the server preference
## 49199 = TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256
## 49195 = TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256
## 52392 = TLS_ECDHE_RSA_WITH_CHACHA20_POLY1305
## 52393 = TLS_ECDHE_ECDSA_WITH_CHACHA20_POLY1305
##
## On non-Intel CPUs such as MIPS routers and ARM systems (Android, Raspberry Pi...),
## the following suite improves performance.
## This may also help on Intel CPUs running 32-bit operating systems.
##
## Keep tls_cipher_suite empty if you have issues fetching sources or
## connecting to some DoH servers. Google and Cloudflare are fine with it.
tls_cipher_suite = [52392, 49199]
## Fallback resolver
## This is a normal, non-encrypted DNS resolver, that will be only used
## for one-shot queries when retrieving the initial resolvers list, and
## only if the system DNS configuration doesn't work.
## No user application queries will ever be leaked through this resolver,
## and it will not be used after IP addresses of resolvers URLs have been found.
## It will never be used if lists have already been cached, and if stamps
## don't include host names without IP addresses.
## It will not be used if the configured system DNS works.
## A resolver supporting DNSSEC is recommended. This may become mandatory.
##
## People in China may need to use 114.114.114.114:53 here.
## Other popular options include 8.8.8.8 and 1.1.1.1.
# fallback_resolver = '9.9.9.9:53'
# fallback_resolver = '8.8.8.8:53'
fallback_resolver = '208.67.222.222:53'
## Never let dnscrypt-proxy try to use the system DNS settings;
## unconditionally use the fallback resolver.
ignore_system_dns = true
## Maximum time (in seconds) to wait for network connectivity before
## initializing the proxy.
## Useful if the proxy is automatically started at boot, and network
## connectivity is not guaranteed to be immediately available.
## Use 0 to disable.
netprobe_timeout = 60
## Offline mode - Do not use any remote encrypted servers.
## The proxy will remain fully functional to respond to queries that
## plugins can handle directly (forwarding, cloaking, ...)
# offline_mode = false
## Automatic log files rotation
# Maximum log files size in MB
log_files_max_size = 1
# How long to keep backup files, in days
log_files_max_age = 1
# Maximum log files backups to keep (or 0 to keep all backups)
log_files_max_backups = 1
#########################
# Filters #
#########################
## Immediately respond to IPv6-related queries with an empty response
## This makes things faster when there is no IPv6 connectivity, but can
## also cause reliability issues with some stub resolvers.
## Do not enable if you added a validating resolver such as dnsmasq in front
## of the proxy.
block_ipv6 = true
##################################################################################
# Route queries for specific domains to a dedicated set of servers #
##################################################################################
## Example map entries (one entry per line):
## example.com 9.9.9.9
## example.net 9.9.9.9,8.8.8.8,1.1.1.1
# forwarding_rules = 'forwarding-rules.txt'
forwarding_rules = 'dnscrypt-forwarding-rules.txt'
###############################
# Cloaking rules #
###############################
## Cloaking returns a predefined address for a specific name.
## In addition to acting as a HOSTS file, it can also return the IP address
## of a different name. It will also do CNAME flattening.
##
## Example map entries (one entry per line)
## example.com 10.1.1.1
## www.google.com forcesafesearch.google.com
cloaking_rules = 'cloaking-rules.txt'
###########################
# DNS cache #
###########################
## Enable a DNS cache to reduce latency and outgoing traffic
cache = true
## Cache size
cache_size = 512
## Minimum TTL for cached entries
cache_min_ttl = 600
## Maximum TTL for cached entries
cache_max_ttl = 86400
## Minimum TTL for negatively cached entries
cache_neg_min_ttl = 60
## Maximum TTL for negatively cached entries
cache_neg_max_ttl = 600
###############################
# Query logging #
###############################
## Log client queries to a file
[query_log]
## Path to the query log file (absolute, or relative to the same directory as the executable file)
# file = 'query.log'
## Query log format (currently supported: tsv and ltsv)
# format = 'tsv'
## Do not log these query types, to reduce verbosity. Keep empty to log everything.
# ignored_qtypes = ['DNSKEY', 'NS']
############################################
# Suspicious queries logging #
############################################
## Log queries for nonexistent zones
## These queries can reveal the presence of malware, broken/obsolete applications,
## and devices signaling their presence to 3rd parties.
[nx_log]
## Path to the query log file (absolute, or relative to the same directory as the executable file)
# file = 'nx.log'
## Query log format (currently supported: tsv and ltsv)
# format = 'tsv'
######################################################
# Pattern-based blocking (blacklists) #
######################################################
## Blacklists are made of one pattern per line. Example of valid patterns:
##
## example.com
## =example.com
## *sex*
## ads.*
## ads*.example.*
## ads*.example[0-9]*.com
##
## Example blacklist files can be found at https://download.dnscrypt.info/blacklists/
## A script to build blacklists from public feeds can be found in the
## `utils/generate-domains-blacklists` directory of the dnscrypt-proxy source code.
[blacklist]
## Path to the file of blocking rules (absolute, or relative to the same directory as the executable file)
# blacklist_file = 'dnscrypt-blacklist-domains.txt'
## Optional path to a file logging blocked queries
# log_file = 'blocked.log'
## Optional log format: tsv or ltsv (default: tsv)
# log_format = 'tsv'
###########################################################
# Pattern-based IP blocking (IP blacklists) #
###########################################################
## IP blacklists are made of one pattern per line. Example of valid patterns:
##
## 127.*
## fe80:abcd:*
## 192.168.1.4
[ip_blacklist]
## Path to the file of blocking rules (absolute, or relative to the same directory as the executable file)
# blacklist_file = 'dnscrypt-blacklist-ips.txt'
## Optional path to a file logging blocked queries
# log_file = 'ip-blocked.log'
## Optional log format: tsv or ltsv (default: tsv)
# log_format = 'tsv'
######################################################
# Pattern-based whitelisting (blacklists bypass) #
######################################################
## Whitelists support the same patterns as blacklists
## If a name matches a whitelist entry, the corresponding session
## will bypass names and IP filters.
##
## Time-based rules are also supported to make some websites only accessible at specific times of the day.
[whitelist]
## Path to the file of whitelisting rules (absolute, or relative to the same directory as the executable file)
# whitelist_file = 'whitelist.txt'
## Optional path to a file logging whitelisted queries
# log_file = 'whitelisted.log'
## Optional log format: tsv or ltsv (default: tsv)
# log_format = 'tsv'
##########################################
# Time access restrictions #
##########################################
## One or more weekly schedules can be defined here.
## Patterns in the name-based blocklist can optionally be followed with @schedule_name
## to apply the pattern 'schedule_name' only when it matches a time range of that schedule.
##
## For example, the following rule in a blacklist file:
## *.youtube.* @time-to-sleep
## would block access to YouTube only during the days, and period of the days
## define by the 'time-to-sleep' schedule.
##
## {after='21:00', before= '7:00'} matches 0:00-7:00 and 21:00-0:00
## {after= '9:00', before='18:00'} matches 9:00-18:00
[schedules]
# [schedules.'time-to-sleep']
# mon = [{after='21:00', before='7:00'}]
# tue = [{after='21:00', before='7:00'}]
# wed = [{after='21:00', before='7:00'}]
# thu = [{after='21:00', before='7:00'}]
# fri = [{after='23:00', before='7:00'}]
# sat = [{after='23:00', before='7:00'}]
# sun = [{after='21:00', before='7:00'}]
# [schedules.'work']
# mon = [{after='9:00', before='18:00'}]
# tue = [{after='9:00', before='18:00'}]
# wed = [{after='9:00', before='18:00'}]
# thu = [{after='9:00', before='18:00'}]
# fri = [{after='9:00', before='17:00'}]
#########################
# Servers #
#########################
## Remote lists of available servers
## Multiple sources can be used simultaneously, but every source
## requires a dedicated cache file.
##
## Refer to the documentation for URLs of public sources.
##
## A prefix can be prepended to server names in order to
## avoid collisions if different sources share the same for
## different servers. In that case, names listed in `server_names`
## must include the prefixes.
##
## If the `urls` property is missing, cache files and valid signatures
## must be already present; This doesn't prevent these cache files from
## expiring after `refresh_delay` hours.
[sources]
## An example of a remote source from https://github.com/DNSCrypt/dnscrypt-resolvers
# [sources.'public-resolvers']
# urls = ['https://raw.githubusercontent.com/DNSCrypt/dnscrypt-resolvers/master/v2/public-resolvers.md', 'https://download.dnscrypt.info/resolvers-list/v2/public-resolvers.md']
# cache_file = 'public-resolvers.md'
# minisign_key = 'RWQf6LRCGA9i53mlYecO4IzT51TGPpvWucNSCh1CBM0QTaLn73Y7GFO3'
# refresh_delay = 72
# prefix = ''
# [sources.'public-resolvers']
# urls = ['https://raw.githubusercontent.com/DNSCrypt/dnscrypt-resolvers/master/v2/public-resolvers.md', 'https://download.dnscrypt.info/resolvers-list/v2/public-resolvers.md']
# minisign_key = 'RWQf6LRCGA9i53mlYecO4IzT51TGPpvWucNSCh1CBM0QTaLn73Y7GFO3'
# cache_file = 'public-resolvers.md'
# urls = ['https://raw.githubusercontent.com/DNSCrypt/dnscrypt-resolvers/master/v2/onion-services.md', 'https://download.dnscrypt.info/resolvers-list/v2/onion-services.md']
# minisign_key = 'RWQf6LRCGA9i53mlYecO4IzT51TGPpvWucNSCh1CBM0QTaLn73Y7GFO3'
# cache_file = 'onion-services.md'
# sdns://AgMAAAAAAAAADjE3Ni41Ni4yMzYuMTc1ID4aGg9sU_PpekktVwhLW5gHBZ7gV6sVBYdv2D_aPbg4DmRucy5hYWZsYWxvLm1lCi9kbnMtcXVlcnk
## Quad9 over DNSCrypt - https://quad9.net/
# Cloudflare DNS (anycast) - aka 1.1.1.1 / 1.0.0.1
# sdns://AgcAAAAAAAAABzEuMC4wLjGgENk8mGSlIfMGXMOlIlCcKvq7AVgcrZxtjon911-ep0cg63Ul-I8NlFj4GplQGb_TTLiczclX57DvMV8Q-JdjgRgSZG5zLmNsb3VkZmxhcmUuY29tCi9kbnMtcXVlcnk
# [sources.quad9-resolvers]
# urls = ["https://www.quad9.net/quad9-resolvers.md"]
# minisign_key = "RWQBphd2+f6eiAqBsvDZEBXBGHQBJfeG6G+wJPPKxCZMoEQYpmoysKUN"
# cache_file = "quad9-resolvers.md"
# refresh_delay = 72
# prefix = "quad9-"
## Another example source, with resolvers censoring some websites not appropriate for children
## This is a subset of the `public-resolvers` list, so enabling both is useless
# [sources.'parental-control']
# urls = ['https://raw.githubusercontent.com/DNSCrypt/dnscrypt-resolvers/master/v2/parental-control.md', 'https://download.dnscrypt.info/resolvers-list/v2/parental-control.md']
# cache_file = 'parental-control.md'
# minisign_key = 'RWQf6LRCGA9i53mlYecO4IzT51TGPpvWucNSCh1CBM0QTaLn73Y7GFO3'
## Optional, local, static list of additional servers
## Mostly useful for testing your own servers.
# [static]
[static.'cloudflare']
stamp = 'sdns://AgcAAAAAAAAABzEuMC4wLjGgENk8mGSlIfMGXMOlIlCcKvq7AVgcrZxtjon911-ep0cg63Ul-I8NlFj4GplQGb_TTLiczclX57DvMV8Q-JdjgRgSZG5zLmNsb3VkZmxhcmUuY29tCi9kbnMtcXVlcnk'
# Cloudflare Onion Service
# stamp = 'sdns://AgcAAAAAAAAAACC0WWFtenR5met-s8i0oiShMtYstulWSybPBq-zBUEMNT5kbnM0dG9ycG5sZnMyaWZ1ejJzMnlmM2ZjN3JkbXNiaG02cnc3NWV1ajM1cGFjNmFwMjV6Z3FhZC5vbmlvbgovZG5zLXF1ZXJ5'
[static.'google']
stamp = 'sdns://AgUAAAAAAAAAAKAe9iTP_15r07rd8_3b_epWVGfjdymdx-5mdRZvMAzBuSB2gCRHoBmTGj8AQwTFP9xsGyw3jcS-j3Ozn9nJad-0RQ5kbnMuZ29vZ2xlLmNvbQ0vZXhwZXJpbWVudGFs'
[static.'cisco']
stamp = 'sdns://AQAAAAAAAAAADjIwOC42Ny4yMjAuMjIwILc1EUAgbyJdPivYItf9aR6hwzzI1maNDL4Ev6vKQ_t5GzIuZG5zY3J5cHQtY2VydC5vcGVuZG5zLmNvbQ'
# [static.'quad9']
# stamp = 'sdns://AgYAAAAAAAAACDkuOS45LjEwgAASZG5zOS5xdWFkOS5uZXQ6NDQzCi9kbnMtcXVlcnk'
添加规则到 cloaking_rules.txt
这里使用的是104.25.183.205 这个电信优化不错
域名.com 104.25.183.205